Easy HTTPs with Caddy
Nginx and certbot too complicated? Use Caddy.

Let's Encrypt has made obtaining SSL certificates very affordable (free!). Setting up the HTTPs server with Nginx proxy and certbot is still not quite straightforward.
There are multiple steps and proofs via ACME protocol that needs to be done right and not easily automated. Besides one time setup, we also needed to make sure the certs are correctly renewed at a regular interval. Then we also need to make sure to set up HTTP to HTTPS redirects and make sure we configure SSL correctly.
I have written about that before. It is not hard but not quite simple as I'd hope for the world that is seemingly HTTPs by default today.
Enters Caddy
The premise of Caddy automatic HTTPS simple. The whole ACME protocol negotiation and cert renew is done entirely in server. There is no need for a separate scripts or scheduler to handle any of the above
That is done via a very simple Caddyfile which could be readily understood.
Using Caddy as a HTTPS Proxy
Three simple parts.
Caddyfile – This is the configuration. If the first line is a domain name, Caddy assumes you'd want to set it up as HTTPs. The next line is where it should proxy the website
docker-compose.yml – Assuming we already run other services as Docker, we'd want to compose it with other servers.
⚠️ Caddy needs a persistent datastore to save the downloaded certificates. We'd always want to map /data into the host path. If Caddy loses this data, it will repeatedly call to Let's Encrypt every time we restart the server, and we may get rate-limited for a few days.
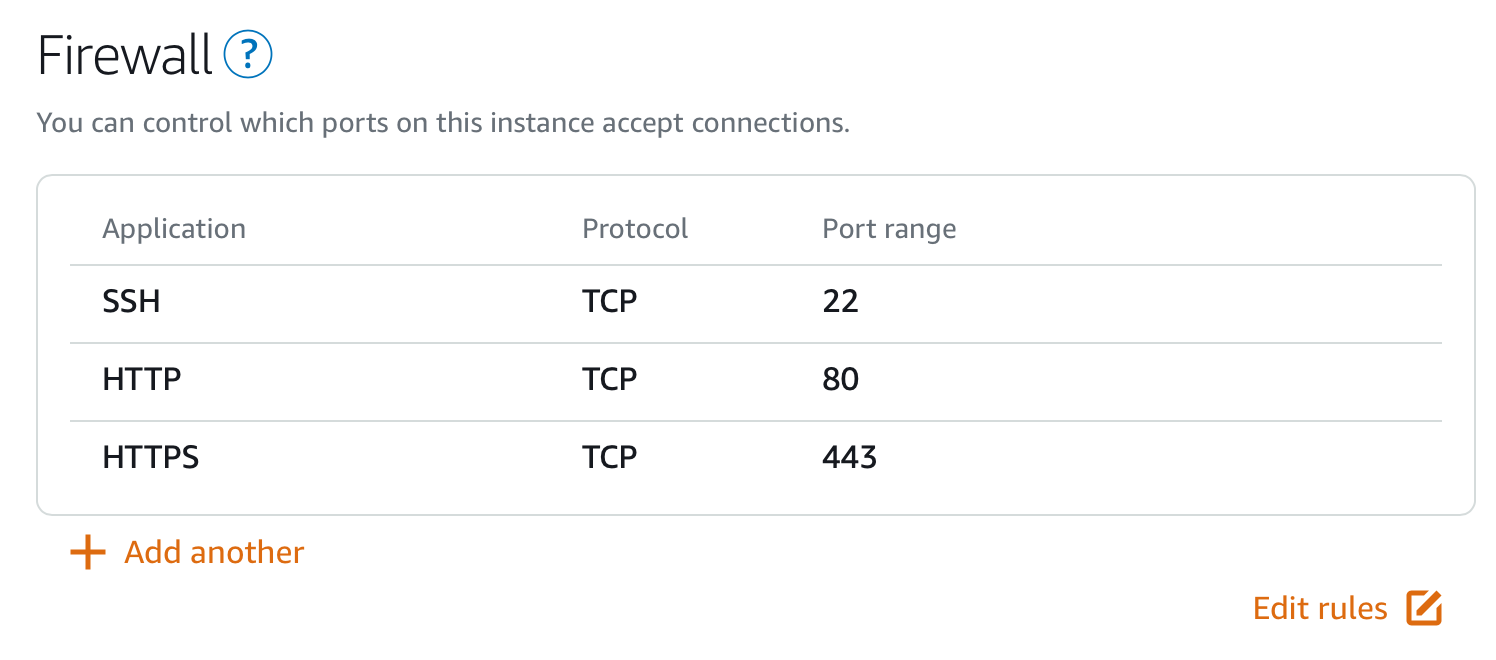
Allow SSL Traffic in Firewall
This depends on our infrastructure. Cloud Providers nowadays provided image with no software firewall (e.g. ufw) but rely on networking configuration in the cloud instead.